Securing voice AI means protecting audio, transcripts, and metadata at every hop—from the caller’s phone to the AI stack and your back-end systems. Strong encryption, tight access control, careful redaction, and disciplined operations work together to keep conversations confidential and compliant.
What gets protected
- Audio: live media streams and recordings
- Text: real-time transcripts, summaries, prompts/responses
- Metadata: caller IDs, timestamps, intent labels, tool actions
- Identifiers: account numbers, addresses, payment details
Encryption in transit
- Telephony signaling: TLS 1.2+ for SIP (SIP-TLS) between carriers, SBCs, and platforms
- Media/audio: SRTP (AES-GCM or AES-CM) for VoIP trunks; WebRTC uses DTLS-SRTP by default
- APIs and webhooks: HTTPS/TLS 1.2+ with modern ciphers and perfect forward secrecy (ECDHE)
- Mutual TLS and IP allowlists: enforce mTLS for back-end integrations (CRM, payment, identity)
- Note on PSTN: legacy phone segments may not be encrypted end-to-end; you secure from the carrier edge inward. For highly sensitive steps, offer a switch to a secure WebRTC session or use DTMF masking.
Encryption at rest
- Recordings, transcripts, logs: AES-256 with envelope encryption (cloud KMS/HSM)
- Customer-managed keys: BYOK/CMK with per-tenant keys and regular rotation
- Segregation: separate storage buckets and keys for audio vs. analytics; object-level access policies
- Backups and archives: encrypted with the same controls; automate rotation and revocation
Minimize sensitive data exposure
- Redaction and masking:
- Pause/resume recording during payment or collect card data via PCI-compliant DTMF suppression
- Auto-redact PII/PHI (names, SSNs, addresses) in transcripts and logs before downstream use
- Tone masking in audio to remove spoken sensitive content
- Tokenization:
- Replace sensitive values (PAN, SSN) with tokens; keep the vault in a PCI/HIPAA-scoped zone
- Send only tokens to LLMs and analytics whenever possible
- Data minimization:
- Collect only what’s needed for the task
- Shorten prompts and summaries to exclude identifiers
Identity, access, and zero trust
- Principle of least privilege with RBAC/ABAC; service accounts scoped per environment and function
- Strong auth for humans: SSO/SAML/OIDC, MFA, device posture checks, just-in-time access, and “break-glass” approvals
- Network controls: VPC peering/PrivateLink, private subnets, egress allowlists, no public data stores
- Secrets management: rotate credentials in a vault (e.g., AWS Secrets Manager, HashiCorp Vault)
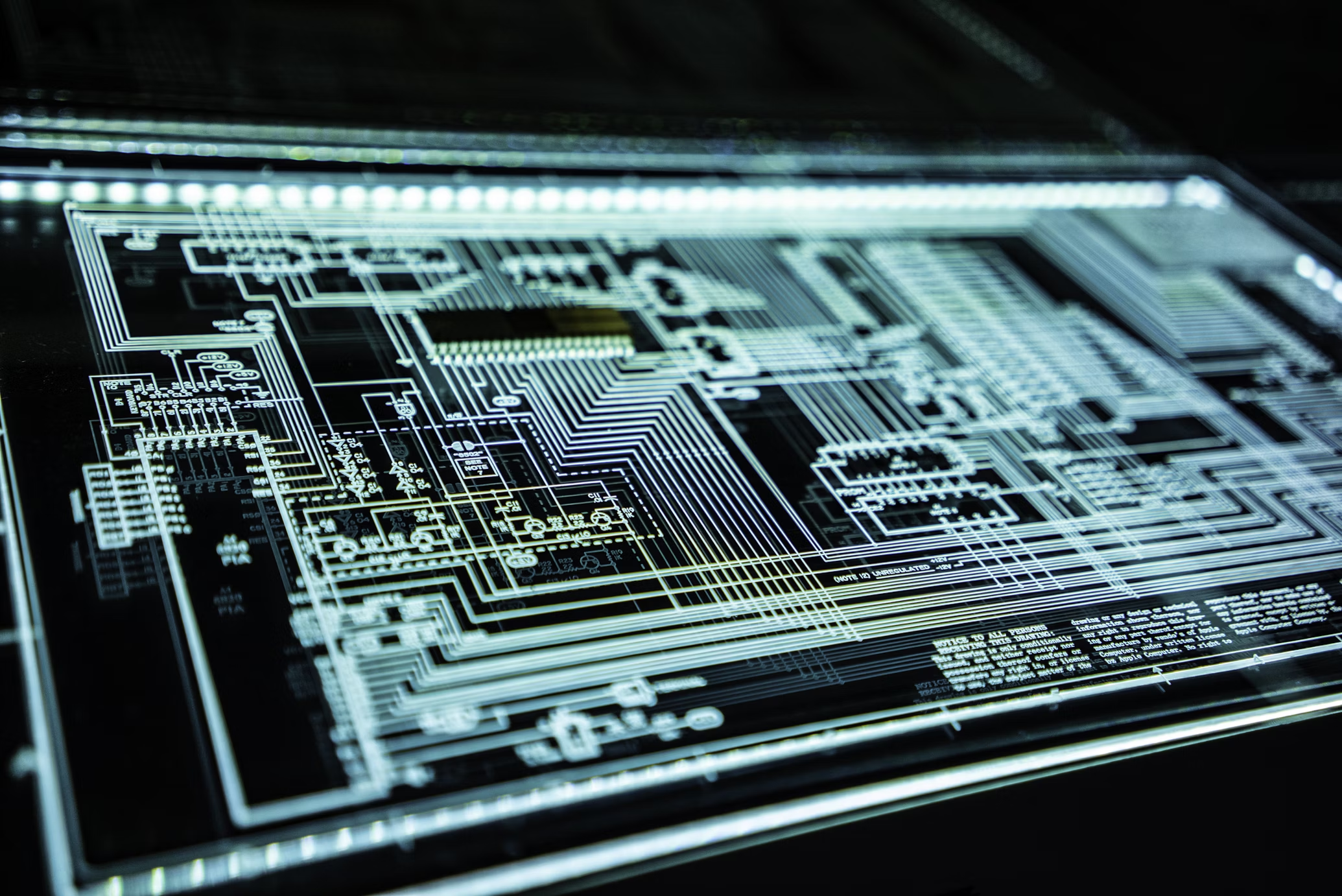
Secure call handling architecture
- Session border controllers (SBCs): terminate SIP-TLS/SRTP, enforce rate limits, fraud/threat protections
- Media relays/TURN: hardened and isolated; DTLS-SRTP for WebRTC clients
- Voice AI processing: decrypt in-memory only; avoid writing raw audio unless recording is enabled and consented
- Retrieval and tools: connect to KBs and APIs over mTLS; cache minimal data with short TTLs
- Payment flows: offload to certified gateways; never expose PAN to LLMs or general logs
Model and vendor data handling
- LLM/ASR/TTS providers:
- Contractually opt out of training on your data; require data isolation and deletion SLAs
- Prefer region-specific processing and data residency
- Penetration tests, SOC 2/ISO 27001 reports, and detailed DPAs/SCCs for cross-border transfers
- On-prem/private inference:
- For highly regulated use cases, consider VPC- or on-prem-hosted models to keep data in boundary
Monitoring, detection, and audit
- Tamper-evident audit logs for access, exports, and admin actions; ship to a SIEM
- Real-time alerts on unusual transcript queries, large exports, or failed mTLS
- Call-level security events: consent captured, redaction applied, payment mode entered/exited
- Synthetic calls to continuously test encryption, consent prompts, and DTMF masking
Compliance by design
- PCI DSS: scope reduction via DTMF masking, tokenization, network segmentation; annual assessments
- HIPAA: BAAs in place, minimum necessary rule, access logging, breach notification workflows
- GDPR/CCPA: lawful basis and consent, data subject rights (export/delete), retention and residency controls
- SOC 2/ISO 27001: formalized policies, change management, vendor risk management, incident response
- Call recording consent: per-jurisdiction prompts (one-/two-party consent), periodic beep tones where required
Retention, residency, and deletion
- Configurable retention policies per data type (audio vs. transcripts vs. analytics)
- Region pinning and data localization to meet regulatory requirements
- Automated deletion workflows and verified erasure for right-to-be-forgotten requests
- Object lock/WORM for regulated retention when necessary, balanced with minimization
Threats to plan for and mitigations
- Toll fraud and SIP scanning: SBC hardening, anomaly detection, outbound call limits
- Man-in-the-middle: TLS 1.2+/1.3 everywhere, certificate pinning/mTLS, no plaintext links
- Prompt injection/data exfiltration: strict tool-use policies, output filters, allowlist retrieval, red-team tests
- Insider risk: JIT access, dual control for exports, detailed audits, periodic access reviews
- Supply chain: vendor SBOMs, patch cadence, attestation, and disaster recovery testing
Operational best practices
- Key rotation: automate rotation (e.g., 90 days) and test revocation paths
- Environment isolation: prod vs. non-prod separation with scrubbed synthetic data in lower envs
- Change management: peer-reviewed IaC, canary releases, rollback plans
- Incident response: runbooks, tabletop exercises, and breach notification SLAs
- Regular pen tests and bug bounty to validate controls
Securing voice conversations is a layered program: modern encryption for every hop, minimized and masked data at rest, rigorous access controls, and operational discipline backed by audits and testing. Build with these controls from day one and you’ll protect customer privacy, meet regulatory obligations, and keep trust at the center of your voice AI experience.